- cross-posted to:
- privacy@lemmy.world
- cross-posted to:
- privacy@lemmy.world
“Temu is designed to make this expansive access undetected, even by sophisticated users,” Griffin’s complaint said. “Once installed, Temu can recompile itself and change properties, including overriding the data privacy settings users believe they have in place.”
That’s just nuts
Yeah, it is. It’s such an extraordinary claim.
One requiring extraordinary evidence that wasn’t provided.
“It’s doing amazing hacks to access everything and it’s so good at it it’s undetectable!” Right, how convenient.
Libmanwe-lib.so is a library file in machine language (compiled). A Google search reveals that it is exclusively mentioned in the context of PDD software—all five search results refer to PDD’s apps. According to this discussion on GitHub, “the malicious code of PDD is protected by two sets of VMPs (manwe, nvwa)”. Libmanwe is the library to use manwe.
An anonymous user uploaded a decompiled version of libmanwe-lib to GitHub. It reads like it is a list of methods to encrypt, decrypt or shift integer signals, which fits the above description as a VMP for the sake of hiding a program’s purpose.
In plain words, TEMU’s app employed a PDD proprietary measure to hide malicious code in an opaque bubble within the application’s executables
So wait, bit-shifting some integers is now considered being malicious? Is that really the defense here? Using that definition just about all software in existence is malicious.
deleted by creator
deleted by creator
I don’t believe his claims without evidence, but having a legit cover for nefarious acts is pretty standard, no?
deleted by creator
Why steal their money when they can both get them to give their money as well data to also sell?
This is why companies like Apple are at least a tiny bit correct when they go on about app security and limiting code execution. The fact it aligns with their creed of controlling all of the technology they sell makes the whole debate a mess, though. And it does not excuse shitty behavior on their part.
But damn
And if they got this past Apple in their platforms. That’s even wilder.
The article linked to the analysis and on a quick glance, it seems to be done entirely against the Android variant of the app. This makes sense because if the alleged actions are true, they’d never have gotten on to the App Store for iOS Apple users… or at least as of a couple months ago. Who knows what kind of vulnerability is exposed by Apple only doing limited cursory checks for 3rd party App Stores.
Shits getting scarier by the day.
deleted by creator
- Dynamic compilation using runtime.exec(). A cryptically named function in the source code calls for “package compile”, using runtime.exec(). This means a new program is created by the app itself.—Compiling is the process of creating a computer executable from a human-readable code. The executable created by this function is not visible to security scans before or during installation of the app, or even with elaborate penetration testing. Therefore, TEMU’s app could have passed all the tests for approval into Google’s Play Store, despite having an open door built in for an unbounded use of exploitative methods. The local compilation even allows the software to make use of other data on the device that itself could have been created dynamically and with information from TEMU’s servers.
Ah yes, delete your original incorrect comment instead of continuing the discussion about how wrong and lazy it was to make, nice.
I’m sure Temu collects all information you put into the app and your behaviour in it, but this guy is making some very bold claims about things that just aren’t possible unless Temu is packing some serious 0-days.
For example he says the app is collecting your fingerprint data. How would that even happen? Apps don’t have access to fingerprint data, because the operating system just reports to the app “a valid fingerprint was scanned” or “an unknown fingerprint was scanned”, and the actual fingerprint never goes anywhere. Is Temu doing an undetected root/jailbreak, then installing custom drivers for the fingerprint sensor to change how it works?
And this is just one claim. It’s just full of bullshit. To do everything listed there it would have to do multiple major exploits that are on state-actor level and wouldn’t be wasted on such trivial purpose. Because now that’s it’s “revealed”, Google and Apple would patch them immediately.
But there is nothing to patch, because most of the claims here are just bullshit, with no technical proof whatsoever.
The study and evidence was already provided months ago
This was also linked in the article if you read it
Here’s the actual relevant part
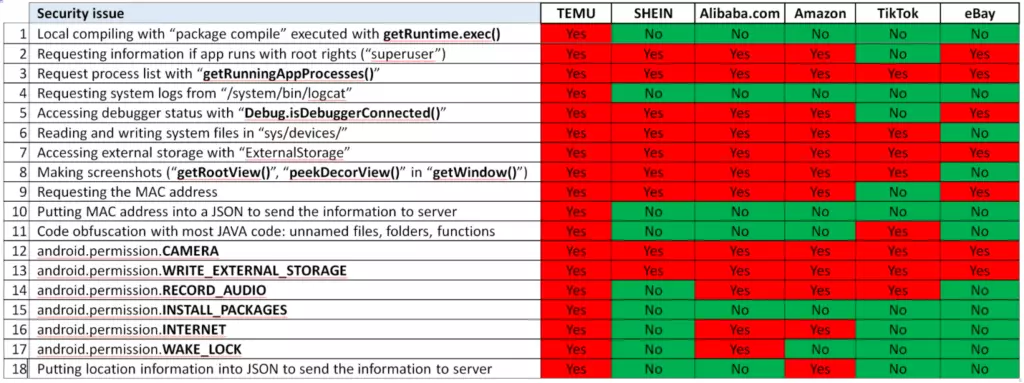
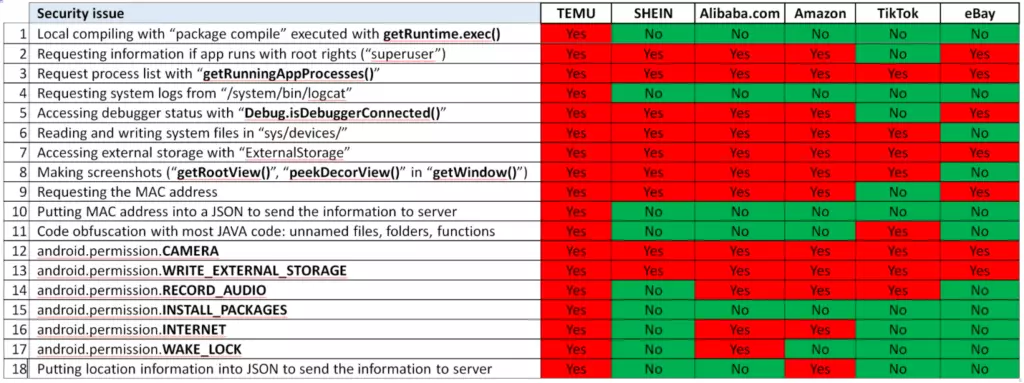
These are security risks to be sure, and while these permissions are (mostly) on the surface, possibly defensible, together they do clearly represent an app trying to gather all of the data that it can.
However, a lot of info from this report is overblown. For example code compilation is sketchy to be sure, but without a privilege escalation attack, it can’t do anything the app couldn’t do with an update.
Also, there’s some weird language in the report, like counting the green security issues in other apps (like tiktok) as if they were also a problem, despite the image showing that green here means it doesn’t present that particular risk.
All of this to say, if you have temu, probably uninstall it. It’s clearly collecting all the data it can get.
But it’s unlikely to be the immediate threat that will have China taking over your phone like this report implies.
This infographic is really helpful. Stuff like this makes me relieved I use the majority of services in a browser, rather than native apps
I’m blown away by how many people use apps when they don’t have to. There’s a reason companies are always trying to get you to download their app, and it’s so they can put their software on your phone and harvest more of your data.
Exactly why I use browser and not apps, too. and if they try to strongarm me with better prices or degraded services, I just stop using them all together.
It’s why I stopped using Reddit on mobile lol. No, I don’t want to download your official app, and no you making it so I need it to access NSFW stuff will convince me to.
Same with X/Twitter. I hate when people put information in those now because you can’t read more than one at a time in some reply to self thread on there without downloading the app. Especially when it’s important news or on the ground reporting. Screw that. All those reporters need to use mastadon.
Yup. I used to watch TikTok’s sent to me. Now I can’t. They want me to use their app. LOL. Nah.
Thanks, that brings done useful context here
That… is not a study by anyone who knows what they are talking about. It also does not mention fingerprints at all.
They seem to believe that the app can use permissions undeclared in the manifest file because they obviously think it’s only for the store to show the permissions to the user. Android will not actually allow an app to use undeclared permissions. The most rational explanation is the codebase is shared with different version of the app (possibly not released) that had different manifests.
It also makes a big deal of checking if running as root. That is not evidence of having an escalation exploit. If they have an ability to get root before running the app why would they need to use the app to exploit it? They could just do whatever they wanted and avoid leaving traces in the app. Though I doubt they would root phones to just brick them. It’s the kind of mischief you would expect from a kid writing viruses, not an intelligence agency or criminal enterprise.
Users who root their own phones are very unlikely to run temu as root. In fact a lot of apps related to shopping or banking try to detect root to refuse to work as your system is unsafely. In any case it’s a very niche group to target.
To keep things short, that ‘study’ does not really look credible or written by actual experts.
The article links to this as technical proof https://grizzlyreports.com/we-believe-pdd-is-a-dying-fraudulent-company-and-its-shopping-app-temu-is-cleverly-hidden-spyware-that-poses-an-urgent-security-threat-to-u-s-national-interests/
There’s analysis of decompiled source code.
The analysis shows it’s spyware, which I don’t question. But it’s spyware in the bounds of Android security, doesn’t hack anything, doesn’t have access to anything it shouldn’t, and uses normal Android permissions that you have to grant for it to have access to the data.
For example the article mentions it’s making screenshots, but doesn’t mention that it’s only screenshots of itself. It can never see your other apps or access any of your data outside of it that you didn’t give it permission to access.
Don’t get me wrong, it’s very bad and seems to siphon off any data it can get it’s hands on. But it doesn’t bypass any security, and many claims in the article are sensational and don’t appear in the Grizzly report.
I agree on the sensationalism in the article.
Still sounds like shitty company doing shitty things
That is not entirely correct. The reported found the app using permissions that are not covered by the manifest. It also found the app being capable to execute arbitrary code send by temu. So it cannot be clearly answered if the app can utilize these permissions or not. Obviously they would not ship such an exploit with the app directly.
The reported found the app using permissions that are not covered by the manifest.
It didn’t found them using them, it’s an important distinction. It found code referring to permissions that are not covered by the Manifest file. If that code was ran, the app would crash, because Android won’t let an app request and use a permission not in the Manifest file. The Manifest file is not an informational overview, it’s the mechanism through which apps can declare permissions that they want Android to allow them to request. If it’s not in the Manifest, then it’s not possible to use. It’s not unusual to have a bunch of libraries in an app that have functionality you don’t use, and so don’t declare the required permissions in the Manifest, because you don’t use them.
It also found the app being capable to execute arbitrary code send by temu.
Yeah, which is shady, but again, there is nothing to indicate that code can go around any security and do any of the sensational things the article claims.
The Grizzly reports shows how the app tricks you into granting permissions that it shouldn’t need, very shady stuff. But it also shows they don’t have a magical way of going around the permissions. The user has to actually grant them.
Do you know if there people who have gone this far analysing the TikTok and WeChat apps?
Yeah, I don’t like Temu, and I’m sure the app is a privacy nightmare, but these claims don’t seem right. If it’s true, I’d like to see someone else verify it.
Wouldn’t the phone have to have your fingerprint stored in order to compare it to the one scanned?
Yes, the phone does, but that data is protected in the hardware and never sent to the software, the hardware basically just sends ok / not ok. It’s not impossible to hack in theory, nothing is, but it would be a very major security exploit in itself that would deserve a bunch of articles on it’s own. And would likely be device specific vulnerability, not something an app just does wherever installed.
Pretty sure this is not true. That’s how apple’s fingerprint scanners work. On android the fingerprint data is stored either in the tpm or a part of the storage encrypted by it.
Yeah, so the app never sees it. What are you disagreeing with?
I just corrected that, can’t I without disagreeing?
I mean that I don’t know what part of my comment is “not true”. I welcome corrections, I just don’t see what is being corrected here.
It doesn’t send a yes/no signal it sends the fingerprint to be compared to the stored one
Temu is absolute cancer in terms of business practices so no surprise here at all.
Cancer in terms of, well, everything.
How about pass and enforce strong digital privacy protection laws you fucking cowards. When other countries spy on us it’s scary and bad, but for US companies? Best we can do is ban porn and demand backdoors to stop E2EE messaging.
California (and a few other states) are trying. The CCPA and CPRA are a good step in the right direction. If you’re a California resident, you can request all the data a business has collected about you, tell them to stop sharing it with business partners, or tell them to completely delete it, similar to the GDPR in Europe.
Oh don’t worry, they’re going to try and kill that too before it hurts them too much, and with the audacity of calling it the “American Privacy Rights Act”. https://www.eff.org/deeplinks/2024/06/eff-opposes-american-privacy-rights-act
Ugh. I hate this so much.
I’m pretty sure Temu is Chinese.
That would hurt the advertising, spam, blackmail, malware, and propaganda industries. We can’t rip out the economic spine of big tech since they pay the best bribes.
Unfortunately they care more about spying on us themselves.
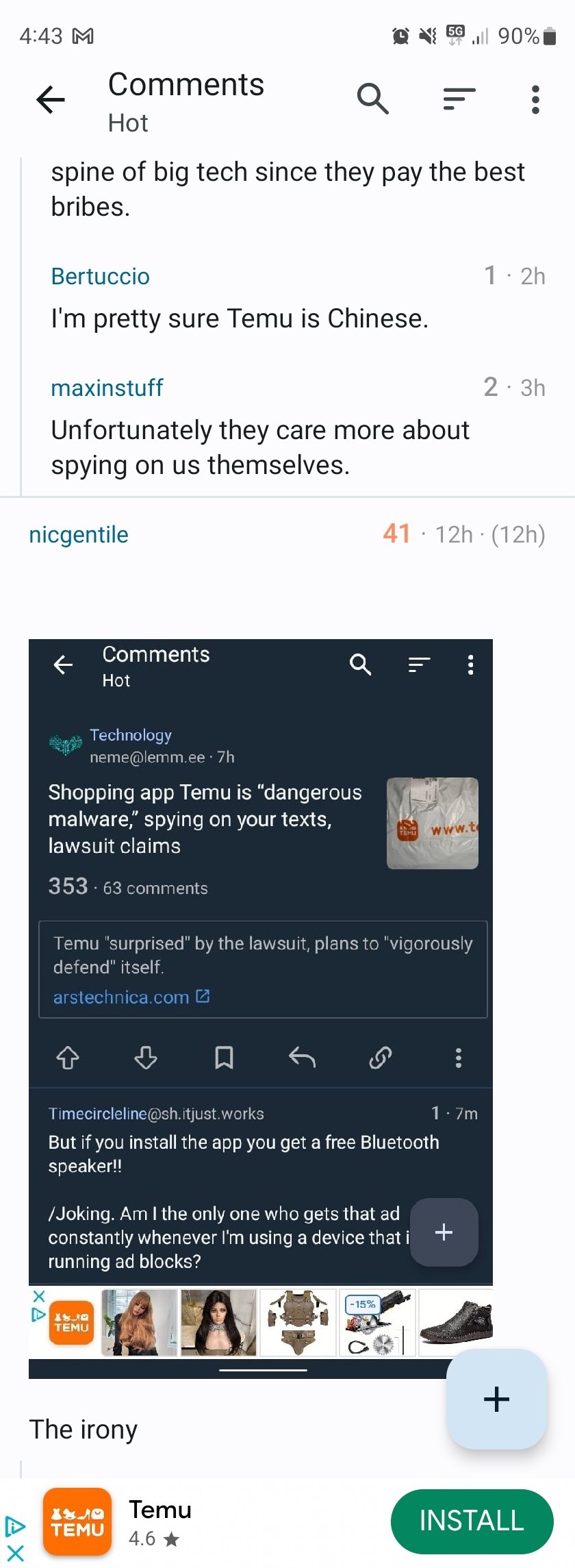
The irony
First, you use Lemmy, that’s great. But pls use a client without ads…
Been using Boost since it was a Reddit client. By default, it is my go to.
Maybe but you’ve done the transition to Lemmy try to use a libre client
I’m all for Libre but in this case @rmayayo@lemmyworld is my leader.
Who is he?
He is the dev who made Boost.
Why does he done it with ads?
100% this. Boost is great
by “client” do you mean “just use a browser”?
Or, you know, the 98% of clients that don’t have ads. I, for one, recommend Voyager.
Maybe but not only, for phone I recommend an app that’s much more optimized for using on mobile
Lemmy website is fine on mobile imo. Not perfect but usable and optimized.
For sure! Personally I prefer using the app
You can pay just a few dollars to remove the ads from Boost.
Bro why using Lemmy if it’s for using proprietary client? Voyager, Jerboa, you have others choice…
Ask the 100,000 people that downloaded Boost, not me.
Probably people who have been using Boost for Reddit before and now want the same experience but for Lemmy
But with this change from reddit to Lemmy the should have done the same thing for their client
Where are you viewing Lemmy posts that you have ads?
I’m using Voyager and it’s great. I don’t even use the app, I prefer the PWA.
I also use Voyager and agree, plus it’s actually open source.
I think it’s the Boost app.
I see; I can’t imagine willingly submitting to ads, but whatever works for them.
Yeah. Boost itself is great though. Well worth the couple of bucks to get rid of the ads forever.
What does Boost have over clients like Voyager?
Ads
Ads for a platform with political views that despise them. Ironic
I use it too. Tried a few different ones and like boost the best. I finally just paid for the non-ad tier. One time cost of 3.99. I would have been turned off by a subscription.
Yeah boost is definitely good, it was my main app until a few months ago. Recently I have been trying Connect, which is another great app.
Connect has improved a lot since I first tried it, also doesn’t have any ads. But all things considered - Boost is bit more polished than connect.
What’s wrong with voyager? Its already ad-free.
Seems so strange to choose to inject adds over top of lemmy by choice.
And it has come a long way too. In fact, I just donated since it’s struck me how solid of an experience it’s been.
That’s what you get for using a proprietary Lemmy app. Switch to Thunder, it doesn’t have ads, it’s open source and in my opinion has the best UI out of all Lemmy apps. Also support the development and join their community: !thunder_app@lemmy.world
From the screenshots alone the interface looks similar to sync
Do you think it’s better than Voyager? That’s what I’ve been using. Pretty satisfied with it.
Jerboa here but same
I tried using Jerboa and found it to be incredibly buggy and poorly designed. Not sure what’s going on there, considering that it’s the official mobile app made by the Lemmy devs
Has worked mostly fine for me, YMMV
Snap! Double irony
Lol
I generally think arstechnica.com does a decent job of being a non-garbage news site. I pay a couple bucks a month for the ad-free RSS feed. This story feels terrible to me. I don’t doubt a law suit has been filed, but I would expect some investigation by the reporter of the extra-ordinary claims of privilege escape the application is claimed to be capable of.
Given that the headline says that it is a claim in a lawsuit, and the lawsuit is by a state attorney general and not some random nobody, I feel like they are being fairly reasonable.
Yes because AG’s from repub states never ever file frivolous lawsuits that suit their own agenda.
I would feel that it would be a reasonable if it was my local paper running the story. Arstechnica IS a primarily technical news site—I believe they should have a higher bar—otherwise they are just parroting a report and not providing useful (to me) news.
Shocked i tell you. I am shocked.
No way an app would collect data it doesnt need. Preposterous.
Next thing you’ll tell me is that tiktok is doing the same thing!
Have any of you actually ever stopped to process what the tagline, “I’m shopping like a billionaire” means?
I’ve always interpreted it as,
I’m needlessly buying things that don’t make me happy, but making the purchase without any hesitation, knowing that the purchase price could never financially impact me in any real way. When I purchase the thing, I’ll probably never use it or actually take it out of the box even. It is just empty, hollow. And somewhere inside, I always know that it’s all only possible, because I’m actively exploiting the cheap labor of scores of other people that are made to perpetually suffer in generations of abject poverty to allow for my relative comfort…
🎶*“I’m shopping like a billionaire!”*🎶
I am disabled and have limited income I don’t have control over increasing or decreasing. I use temu to save a lot of money on essential things that should be cheap but are still overpriced in America. Sponges. Rags. Soaps. Pens. Tools. Home improvement hardware. Plant grow supplies. Gifts for me nieces. The tagline, is just a tagline. Billionaires are not like me and scouring for cheap magic sponges.
Edit: also, temu did not invent drop shipping. Shopping on amazon is literally the same thing.
Good to know people that are disabled don’t mind using shitty maleware apps, I guess?
What’s your point combining using the malware app with you being disabled? Is that supposed to make the app better somehow?
You’re not special because you’re disabled. Things you use aren’t magical amazing. You’re still the same as everyone else.
That’s… not what they were saying? They were responding to a comment saying it encourages consumerism by saying that they use it for better prices on things they need regardless
What does being disabled have to do it?
That’s why they’re broke
Well this disabled person thinks you’re a dumb asshole.
For what reason exactly?
Other commenters have already corrected your thinking, don’t pretend like you didn’t read them.
I completely forgot about this post. I’m not going to read any more comments than I did however long ago the conversation originally was. Oh shit it’s almost 2 weeks old lmao I don’t give a fuck
My interpretation of that tagline is that since the prices on Temu are cheap, it means you can shop as if you had a lot of money, without actually spending that much.
I think you cracked the case on that one, that’s gotta be what it means.
All I want to know is what do these Temu people think my life is like?

Are you a busty outdoorswoman?
I mean, you’re obviously a sexy military mechanic woman, who goes into battle with fantasy battle armor and goes fishing as a hobby! Duh.
The bearings combined with the wrenches made me think, like, roboticist. So maybe they make fishing robots that double as sexbots?
Trust me, fish dont need to be robots to be fucked…
Any good RPG has a solid fishing mini game tbh
I was wondering what that blue thing was. I thought it was a weird personal tool…
It looks like an archery release, used by compound bow shooters to pull the bow string back and release with a trigger or button
Weaponized fishing for covert military operations.
Code Name: Go Fish!
Clearly you use adbloker or something cause temu just got excited when you opened up the link.

It just thinks you’re a garden variety redneck.
Your life looks pretty sick to me!
he’s batman
Batwoman
Batmare
No, you don’t get it.
These massive Batman pecs need support.
Bustybats
deleted by creator
Yesterday, I saw a Temu ad for something and I just wanted to open it to read the info and there were so many popups and “spin the wheel for a prize” and “enter your email here” and so on that I gave up and just looked for the info elsewhere. Never clicking on a Temu link again.
I get their CAPTCHA where I have to slide the puzzle piece over to look at one of their ads. More than half the time I will do this and it will fail saying I didn’t do it right. So yeah temu has become a trash site.
That CAPTCHA isn’t specific to Temu.
one of the best decisions you’ll ever make, next to dns level blocking it on your network.
I’m shocked, I say. Shocked!
The idea of an app being used to gather additional datea from a customer!“Additional date”
Comments here: “Yeah right, I’ll believe it when they explain how.”
Article: literally has a section explaining how
Edit:
Replies: “Yeah, but that’s just a summary. I’ll believe it when they explain in full detail.”
Article: literally has a link to the detailed explanation
The claim is they completely bypass all Android and iOS security is pretty unbelievable.
If so then the real discussion is how these zero day exploits are just sitting around.
EDIT: It seems the focus is on Android but all the information is nonsensical, like AI generated buzzword bingo.
That source looks better indeed.
Ars quotes nonsense like “bypasses the security” and “exploit the user”.
Those terms have meaning and they aren’t applicable here.
At the end though they do say things like
is able to hack your phone from the moment you install the app
Without any credible evidence.
It states that it’s somehow breaking the permissions sandbox by dynamically recompiling code after the app is opened. Unless there is some undisclosed exploit that it’s using to break the sandbox, it’s outside most people’s understanding of how these platforms work
It only explains how it would pass (automatic) reviews. Not how it would bypass the sandbox. So yeah, you’re right, not enough info sadly.
Someone else posted this report in this thread which does a good job of the deceptive practices and API calls the app uses to trick the user into giving permissions up willingly and otherwise collect data it shouldn’t.
Also fuck their landfillware Chinesium “products”.
That’s also most of what’s on Amazon these days.
Amazon is just faster shipped temu garbage
Every person I’ve heard hate on temu shops on amazon, too. It’s pretty ironic.
If it’s $5 and some random assortments of letters for a brand name you might as well just light your money on fire whether you order from temu or amazon or Walmart for that matter
I mean, some things are just fine when they are the cheapest?
Like a worse AliExpress
Can someone explain to me how you can just simply program something to bypass privacy and security features? What is the point of having these features if you can literally just program something to ignore them? Like…??? Temu is obviously bad if this is true, but if it IS true, it shouldn’t have been possible to begin with!!
Im not sure how they specifically bypass the features in other ways but I imagine some of it is from users accepting permissions under the guise of another use. For example, maybe you accept the microphone permission on tik tok to record video. With that permission in theory the app could now use it maliciously. Of course it should all depend on the users choice for that and im not sure beyond the scope of that.
TORfdot0 shared this comment below:
Someone else posted this report in this thread which does a good job of the deceptive practices and API calls the app uses to trick the user into giving permissions up willingly and otherwise collect data it shouldn’t.
By exploiting unknown vulnerabilities in the operating system.
Looking forward to someone answering this
one of the most obvious ways is to simply not bypass them, and then do it from within the application itself. That way you can essentially man in the middle the rest of it, though this would require a rather specific set of events and a particularly nested design of an app.