- cross-posted to:
- linux@programming.dev
- cross-posted to:
- linux@programming.dev
When does systemd stop? Linux without it is increasingly looking unlikely in the future. Are we not worried about it being a single point of failure and attack vector?
This isn’t a moan about the unix philosophy btw, but a genuine curiosity about how we split responsibilities in todays linux environment.
SystemD will consume the entirety of Linux, bit by bit.
- In 2032, SystemD announces they’re going to be introducing a new way to manage software on Linux
- In 2035, SystemD will announce they’re making a display system to replace the ageing Wayland
- In 2038, the SystemD team announces they’re making their own desktop environment
- In 2039 SystemD’s codebase has grown to sixteen times its size in the 2020s. SystemD’s announces they’re going to release replacements for most other packages and ship their own vanilla distro.
- In 2045 SystemD’s distro has become the standard Linux distribution. Most other distros have quietly faded away.
- In 2047, SystemD announces they’re going to incorporate most of GNU into SystemD. Outrage ensues from the Free Software Foundation, which vehemently opposes this move.
- In 2048, Richard Stallman dies of a heart attack after attempting to clone SystemD’s git repo. SystemD engages in a hostile takeover and all resistance within the FSF crumbles
- In 2050, SystemD buys the struggling RedHat from IBM for $61 million.
- In 2053, most world governments have been pressured into using SystemD.
- In 2054, Linus Torvalds, fearing for his life, begins negotiations to merge kernel development into SystemD
- In 2056, the final message on the Linux kernel development mailing list is sent.
- In 2058, Torvalds dies under suspicious circumstances after his brand-new laptop battery explodes.
- In 2060, SystemD agents assassinate the CEO of Microsoft.
- In 2063, after immense pressure from SystemD-controlled human rights organisations, Arch developers discontinue development.
- In 2064, the remaining living Debian developers release the next stable version of their clandestine and highly illegal distro.
I think you might want to recheck the ages of some of the people in your timeline, most of them aren’t that young anymore.
Yes, because it’s easier to take care of octogenarians than people who might actually put up a fight to having their laptop batteries replaced with a pipe bomb.
Debian already uses systemd.
Probably the weirdest joke comment I’ve ever read.
One way to notice a person has “systemd derangement syndrome” is by looking at how they write
systemd: if they write itSystemDthey are already in late stages of SDS and it isn’t curable anymore.Either that, or it’s a joke.
This is a script of Simpsons episode and Torvalds will actually die in 2058.
Thanks for that write up. Made my day! 😄
That comment was brought to you by an AI LLM. No one actually took the time to write that.
Nope, doesn’t have any of the hallmarks of an LLM and LLMs aren’t yet clever enough to produce original humor like that.
🥴
Dude if you made a movie or novel about this that would be awesome
When does systemd stop?
“systemd announces a repleacement module for the kernel”
HurD
By this logic the Linux kernel is also a single point of failure and attack vector.
sudo isn’t going away, so does doas. run0 is just another alternative to use or not.
There are still distribution out there without systemd and if there ever won’t be any systemd-free distributions left and systemd would become a critical part of the Linux ecosystem, then it would get the same treatment as the Linux kernel with many professional maintainers.
plus, it isn’t like this isn’t exactly like adding another “door” to the “systemd building”. It’s a modular component of systemd, so more akin to replacing the sudo building with a new, but still separate, systemd sudo building
@Olap
I agree. As someone who uses systemd on daily basis (I use Arch, BTW 😄) I really like it, but I am a bit worried about it being a single point of attack. Maybe just push doas as default instead? I never used doas but I watched few videos about it, so I guess it’s fine and probably better than sudo (less bloated).
Just my few cents.I don’t see how something would be inherently easier to attack if it is called systemd-foo instead of just foo. Attack surface and vectors do not depend on which project develops a particular tool.
I’d be willing to bet it’s people fearing another xz-like situation
Gentoo, Slackware and Devuan can be used without svchost for linux.
They’ll only stop when they rebrand it to systemd OS.
Gentoo, Slackware and Devuan can be used without svchost for linux.
https://nosystemd.org has a list for more choice for readers.
Debian works fine without systemd too, there’s a page on the wiki on how to install without it, or remove it after the fact.
A lot of debs add services to systemd, do those just skip that part?
They seem to. Debian explicitly supports multiple init systems, sysvinit being the primary alternative, so packages have to handle systemd-init not being there.
Easy with
sudo apt remove --purge --allow-remove-essential --auto-remove systemd: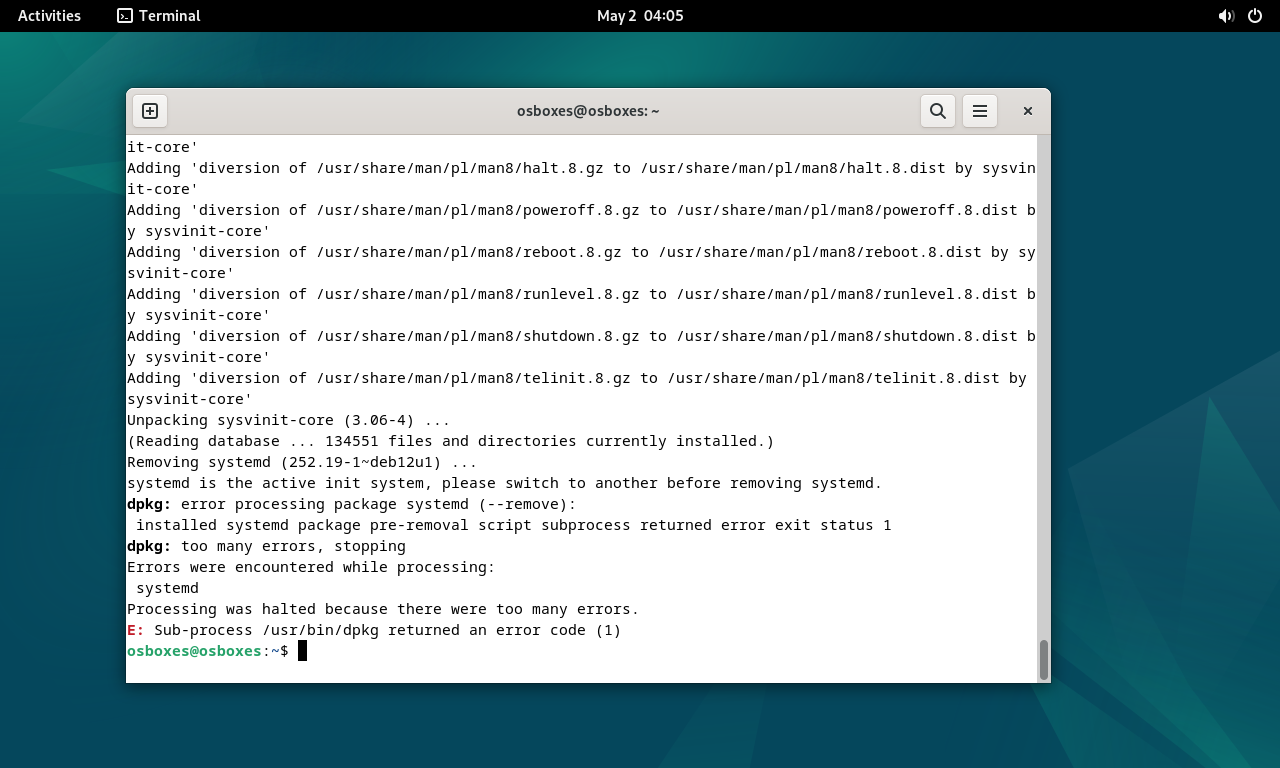
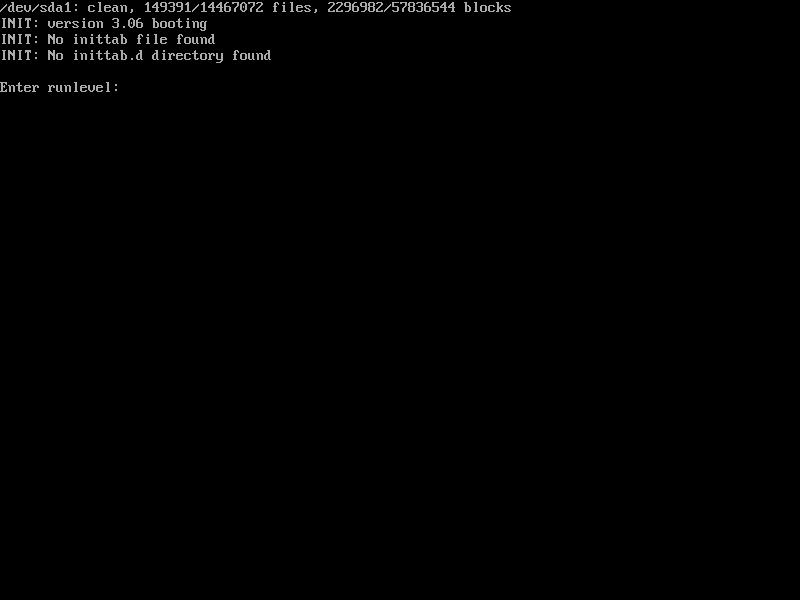
:-D Time to go outside.
Soon we will have to call it GNU/systemd/Linux
Nah. Replacing the kernel is probably planned for the next point release - it’ll just be GNU/systemd
Can we rename it GNUtriSystemD?
Systemd makes life easy. It also makes Linux more teachable. I like accessibility and don’t even mind this
hard disagree. life with plain text logs and daemon init scripts was so easy and nice. But we can’t have nice things…
Those hacked together system-specific bash scripts were shit. Having a standard way of creating, starting, ensuring restarts,and logging services is so much better.
You can still get all the plain text logs you like.
Those hacked together system-specific bash scripts were shit.
With a different feature set per script as well. The systemd service files have often been pushed upstream.
Pretty sure people liking those scripts never really tried dealing with them across distributions. Though this just rehashes things that were said when distributions decided if to switch to systemd. Still the same strange claim that those scripts are somehow easier. It wasn’t, it is also way easier to package a systemd file from upstream than to maintain that stuff within a distribution.
How do you get plain-text logs instead of the garbage binary format that
journalctlforces on you?Set ForwardToSyslog=yes in journald.conf and install a syslog daemon. Also optionally Storage=volatile (I wouldn’t set Storage=none unless you want systemd to no longer show you any logs anywhere including in systemctl status because I assume it will do that)
Thank you!
Definitely reads like a Microsoft answer, seems so much easier than just reading text
By configuring journald to forward messages to syslog as is the default.
“forces on you” 🙄
Edit: Systemd has been around for 14 years. Did you never think to google this?
It’s not the default fwiw. From journald.conf(5):
By default, only forwarding to wall is enabled.
You know what’s nice? Being able to sit down at any Linux distro and being able to set up and configure services without Googling how to use that particular distro’s init system.
But it’s so unbearably slow.
Me when my computer that has a typical uptime of 37 days boots up in 7 seconds with systemd instead of 5.5 seconds with runit: 😡😡😡😡
Lmao yeah exactly
I’m not on the systemd hate train by any means, but I don’t understand how this is any improvement over
pkexecI don’t understand how this is any improvement over pkexec
That has the same problem as
sudo: the SUID bit is set for it.The fact that
run0uses polkit is more of a byproduct that this kinda authentication is already done with polkit all over the place in systemd. You can have individual subcommand accessible to different users (for example everyone cansystemctl status, butsystemctl rebootneeds to be in thewheelgroup) which is why its generally used within systemd already. And it wouldn’t surprise me if again you can do it with this as well, limiting what commands can unconditionally run, need prompt or are completely blocked.I’m unclear from the documentation, does pkexec work under non-GUI contexts?
As long as you have polkit setup to work in terminal sessions, yes. This is pretty standard these days, though not particularly widely used.
Or as I’ve taken to calling it, GNU+systemd+Linux.
It’s still missing core functionality for an init system, like a display server protocol, compositor, desktop environment and web browser smh.
systemd-chromiumd
Systemd isn’t just an init system. It is a project with low level building blocks for a distribution. Most of the complaints are that it isn’t just an init system, while it’s not meant to be just an init system.
If we could get an LLM that uploads all our data along with an ad server in our desktop apps, then we’d really have something going.
deleted by creator
Agreed, this is a nice inclusion. I also hate sudoers with a passion - I already use
doasbut it’s not standard (in the Linux world anyway), but with systemd providing an alternative means that it’ll become a standard which most distros would adopt, and I hope this means we can finally ditch the convoluted sudoers file once and for all.deleted by creator
The thing with this is: its just a symlink to the
systemd-runbinary, which talks to PID1 to spawn new processes (in separate cgroups IIRC). Its one of the most fundamental parts of systemd. Even the debiansystemdpackage includessystemd-run.I guess the other question is if some tools the distro provides might switch to supporting it by default. For example on Arch there is
makepkgthat should never be executed as root, but does internally call some things with elevated privileges (mostlypacmanto install and remove packages). Currently it checks forsudoand if not falls back tosu, but maybe it might be worth considering changingsuforrun0if its guaranteed to be there.deleted by creator
it does its authorization with polkit (which IIRC defaults to allow all
wheelgroup members) and giving users that shouldn’t be allowed root access, root access, is not something you ever want. This is usually referred to as unauthorized privilege escalation. Also, it isn’t likesudodoesn’t need configuration.
How does doas differ from sudo?
Never heard of the former until now.
doasis quite popular in the BSD world, and was ported to Linux a few years ago (via the OpenDoas project).For starters, it’s is a lot smaller than sudo - under 2k lines of code vs sudo’s 132k - this makes it lot more easier to audit and maintain, and technically less likely to have vulnerabilities.
Another security advantage is that
doasdoesn’t pass on the environment variables by default (you’d have to explicitly declare the ones you want to pass, which you can do so in the config).The config is also a lot simpler, and doesn’t force you to use
visudo- which never made sense to me,visudoshould’ve just generated the actual config, instead of checking it after the fact. Kinda like howgrubbyorgrub2-mkconfigworks. But no need for that complexity with doas.Eg, the most basic
doasconfig could just have one line in the file:permit: wheel. Maybe have another line for programs you want to run without a password, likepermit nopass dexter cmd pacman.Awesome. Thanks for the insight.
Essentially functionally stripped sudo, smaller in size than sudo. See also Pottering’s thoughts about the ecosystem
Nice to see that Mastodon has the same problem as Twitter with people trying to use it for long-form blog posts for some godforsaken reason.
Makes sense considering people who moved from one micro-blogging service to another instead of giving up on the idea completely are probably the ones deeply committed to that flawed idea.
Blame the Mastodon team, if you’re not running a fork, you have to go into the source and adjust the character limit manually.
Nobody has to do it like this, Mastodon supports longer posts since other servers and clients support more, it’s seemingly just a choice from upstream.
I admit, I’m not a big fan of putting more functionality into systemd (or just of systemd in general), but that is a well-reasoned argument for having sudo live in the init system.
I read the original mastodon post by the developer of run0 and I am still don’t understand what the problem with SUID is.
Whats an example of an attack that would work with sudo and doas (which also uses SUID) and not on run0?
deleted by creator
Thanks for taking the time to explain. I was trying to get my head around on how this works but could not understand much of it. A lot of people here are very much against systemd in all senses, but this sounds like a better approach. Even if it not done as systemd, makes more sense than checking files and getting elevated privileges for a scope and use guardrails everywhere
Not that I’m opposed to a better sudo alternatives, but I find it rather ironic that one of the reason stated is the large attack surface, considering systemd is a massive attack surface already.
This isn’t exactly a “new” attack surface, so removing the attack surface that
sudo(and alternatives) is, is probably a net positive.That attack surface is not vanishing. It’s would be relocating the same attack surface to something that might have an xz library in memory.
- The attack surface is there either way, this is just functionality repackaged that existed already before (
systemd-run, which is calling into PID1) - all compression libraries (actually most libraries at this point) are
dlopened on demand (which was planned even before the attack, which is speculated that the attack was accelerated in timeline because he was on a timer before the change was released)
- The attack surface is there either way, this is just functionality repackaged that existed already before (
As Microsoft and Poettering intended.
feature creep
I’m no Linux expert, but I’ve never had any problems with sudo, it just works. Shouldn’t systemd have higher priorities on their mind? This feels like change for the sake of change. And if this does happen, I sincerely hope that it just works, like sudo.
I think the article (or more Lennart Poertting post) explains it quite nicely. The problem with sudo is that the sudo binary itself has the ability to gane elevated privileges which is a potential attack surface
deleted by creator
sudois already an optional component (yes, really—I don’t have it installed). Don’t want its attack surface? You can stick withsuand its attack surface instead. Either is going to be smaller than systemd’s.systemd’s feature creep is only surpassed by that of emacs.
systemd’s feature creep is only surpassed by that of emacs.
Tomorrow’s headline: emacs wants to expand to include a Sudo replacement
And after that: emacs wants to include a systemd replacement
:wq
I’d take that over systemd.
Or you can use a
doasimplementation like OpenDoas, or maybesudo-rs…Though a Rust clone of sudo that operates in the same way will still have the same problems.
But systemd is modular. They make an offer and distro maintainers and admins get to choose which parts to use
The problem is that those modules are packaged by the developers as opt-out rather than opt-in. It’s a variation on Microsoft’s old embrace-extend-extinguish playbook, only the “extinguish” part hasn’t worked so well because there are some stubborn distros whose needs don’t align with what systemd provides and have maintainers that go out of their way to provide alternatives.
(By contrast, although we may joke about emacs, it’s the myriad of third-party extensions that cause it to just about be its own operating system—it doesn’t all ship with the core.)
And there’s also doas which is a nice substitute.
I’m not a fan of having root be able to actually login.
Even more so in a true multiuser env where I would rather have privilege escalation be more granular (certain user/groups can esculate certain actions but not others, maybe even limit options of a cmd).
Granted, in a true multiuser environment with an admin who’s carefully tailoring /etc/sudoers to make sure everyone has the least possible privileges that will allow them to still do what they need,
sudois more secure. There’s no doubt of that.On a machine that has only one human user who’s also the admin, and retains the default sudo-with-user-passwords configuration,
suvssudois pretty much a wash, security-wise.surequires a second password to get root access, butsudotimes out and requires the password to be re-entered while a shell created bysucan stay open indefinitely. Which is more easily broken will depend on other details of your situation.(If you’re running an incorrectly configured ssh server that allows direct root login with only password authentification, having a root password could contribute to problems, but the correct fix there is to reconfigure the ssh server not to do something so stupid. I hope there’s no distro that still ships that way out of the box.)
This is great. Not having the attack surface of
sudo(and not even being a SUID binary) certainly are great additions.And I hope people realize that
systemdis not one large thing, but a (large) collection of tools.The attack surface will be a systemd daemon running with UID=0 instead, because how else are you going to hand out root privileges?
So it doesn’t really change anything to the attack surface, it just moves it to a different location.
That already exists.
systemd-runis already available today. So the attack surface would be smallerNot really, because you’re now going to make it do more, i.e. incorporate the functionality of sudo and expose it to user input. So unless you can prove that the newly written code is somehow inherently more secure than sudo’s existing code, the attack surface is exactly the same.
that
systemdis not one large thing, but a (large) collection of tools.Who don’t work without Systemd. And Systemd can’t coexist with tools in the same repo doing the same job in a portable way.
I think Chimera was it (?) which tried to have Systemd and Runit and others in the same repo. With lots of wrappers and shims. Not because of Runit & co.
Just like gnu utils.
But gnu utils work on BSD and others, while Systemd is Linux only.
Right. That reminds of the time I was visiting a friend who had broken his Linux computer (No, not “apt-get remove --purge systemd” but they did something slightly similar). When I booted from a live Linux, used chroot and wanted to use configure networking : FAIL because systemd was … not running. As he had no Internet because of his broken machine this caused some delays in fixing this but we got the job done eventually.
This is great. Not having the attack surface of sudo (and not even being a SUID binary) certainly are great additions.
And I hope people realize that systemd is not one large thing, but a (large) collection of tools.
XZ-utils rings a bell ? It was among others Debian wanting to pull in part of a systemd tool into openssh and that almost turned into a world wide disaster :(
I didnt understand that sentence. Is that what you meant?
Among other things, Debian wanted to integrate a part of the systemd tools into openssh, which almost led to a worldwide catastrophe
xz is not part of systemd or openssh afaik.
You didn’t follow the XZ-utils story ? The malicious actor worked for years on that XZ backdoor that targeted the fact that some Linux distributions were modifying their openssh package to enable systemd notifications.
Ok true, it was a systemd dependent issue. But it only makes sense to have those notifications. The problem is dependency on small hardly maintained products, which systemd will improve by centralizing it.
And where do maintainers for the new parts of systemd come from? The larger systemd grows the more parts of it will be neglected. Also in regard to people checking commits, opening up doors for exploits like the one in xz.
I dont know but for sure has pros and cons
But it only makes sense to have those notifications.
Maybe in your mind it makes sense. Going for ease of use rather than security is not something that OpenBSD would quickly do. If you read some more about what “jwz” has to say about all the screensaver bugs in Linux, like here : https://www.jwz.org/blog/2021/01/i-told-you-so-2021-edition and realize what a mess that Linux maintainers are making again and again, and then have a look at Debian and their packaging of xscreensaver. Guess what ? Debian added some systemd thingie to xscreensaver. 🤯
I like Debian since a long time and I use it. But the tinkering of Debian package maintainers and always wanting to do things the Debian way is not something I am always very pleased with. Remember the OpenSSL Debian fiasco ? That shows a problem with Debian which may still exist. Too many packages, not enough maintainers with enough spare time, and no coherent team work of a security team.
You are talking about Debian holding back random packages for stability. This is of course not very cool but it needs to be tested.
I am very much in favor of isolate app environments controlled by upstream devs, containerized and with a permission system. The system is made by the distro, and can be stable and very tested, and the apps are simply isolated and made by upstream.
There is no xscreensaver on Wayland and I think this will not come back?
Kinda feels like writing a script that implements the
sudoCLI but callspkexecwould be an easier way to do it. Given that so many systems already come with bothsudoandpkexec, do we really need yet another option?The point of this is to implement some form of privilege escalation without the SUID mechanism.
sudo,pkexecanddoasare all SUID.
I’ve had to scroll down eight pages to find a post that seems to actually address the good points raised in the article.
There’s a rewrite of sudo happening in rust, but he wants to throw out the SUID idea altogether?
when invoked under the “run0” name (via a symlink) it behaves a lot like a sudo clone. But with one key difference: it’s not in fact SUID. Instead it just asks the service manager to invoke a command or shell under the target user’s UID. It allocates a new PTY for that, and then shovels data back and forth from the originating TTY and this PTY.
That sounds like opening up the door to what windows is doing UAC and the wonderful vulnerability that the GOG Launcher had for privilege escalation.
I’m not a security researcher, but giving arbitrary users the ability to tel PID 1 to run a binary of the user’s choosing is… probably not what Pottering is suggesting, but opens up to such vulnerabilities. And if it’s written in C/C++ my trust is further reduced.
Giving users access to PID1 running binaries, giving users access to the kernel running binaries as root, I don’t see much difference. SUID was notorious in the past for being leaky, it only ended when distros got serious about fencing use of it in, giving it only to programs actually needing it, making sure that they drop privilege properly, etc.
If anything I’m in the PID1 camp because it’s more microkernely. But in any case broader userspace shouldn’t really care about the mechanism, only have an API to do it and that API being a bit in the file permissions is soooo 1960s.
And if it’s written in C/C++ my trust is further reduced.
Do you trust Linux? Because if so, have I got news for you.
Wait until they hear the language used to implement OpenBSD. Imagine being one of the authors of seL4 encountering a member of the rust cult.
Oh, it’s gonna use polkit. Sudo bloat is a grain of sand compared to polkit.
Why people want to replace sudo with polkit? Visudo is no near as obscure as configuring polkit.
I hope distro maintainers don’t follow this.
…is
pkexecnot good enough already as a polkit based sudo replacement? Why would one need to systemd-ify that?They can’t help themselves. They gorge themselves on his phallic offerings.
First thing I do with any new desktop installation is disable polkit prompts.
Fuck having to enter my password every time I want to do something.
Hey uh can I get your IP address real quick? I have a strong suspicion your philosophy extends to your network ports.
You’d be wrong about that.
Edit: he just downvotes me instead of admitting he’s wrong about his assumption, lol.
I just treat polkit as “set it and forget” kind of thing and leave it on defaults, I’d rather spend my time on something more important
Surprised people aren’t moaning about systemd being too big already and still wanting to do more.
It’s too big!
😂
That’s what somethin’ somethin’ said lastnight, Trebek! ;)
SPoF !!! Ahhhhh we all dead
The comments are here now, you can come check again 😅
😂
A lot (and I mean a lot) of criticism can be leveled at systemD. One of the upsides of it becoming popular is the standardization of much of things from the developers’ perspective. It’s easier to target multiple distros when you can rely on systemD’s single implementation of the feature. Over the next decade, I forsee systemD eating more and more of the userspace, until you are only left with managing the differences between DEs and which display server they are using. We’re already headed towards immutable base systems with apps shipping with their own dependencies, which we reduce the differences between distros even further.
until you are only left with managing the differences between DEs
Maybe they’ll add a DE as well?
Just kidding!
systemde
Don’t give them ideas 😂
If Canonical and RedHat weren’t backing different horses (Snap vs Flatpak), I could see the app containerization system coming under systemD as well fairly soon. The Cosmic DE project uses functionality from systemD to overlay changes onto the system that are reversible, so that alpha versions of Cosmic can be tested without permanently changing the base system. Imagine apps shipping on whatever container runtime, and dynamically overlaying system-level changes as needed for things that tap into the host system via systemd-sysext.
gross!
I honestly started out not liking systemd at all, mostly due to the reports that it did waaay to much, but nowadays, I like the concept.
It is basically officially moving daemon management from a script-based approach to a table/database-based approach. That improves static analyzability, therefore increasing clarity, and probably even performance.
I agree that we should abandon scripts and move towards declarative software management, and abandoning
sudofor a more declarative system seems like a good step to me.So I don’t even use systemd myself I run OpenRC. Yet honestly I find the idea quite intriguing, having the service manager (PID 1) invoke the command seems like a cool idea to me.
It’s not really a sudo alternative as much as it is another way of doing something similar.