Video shot from a getaway car shows how SIM swappers have snatched worker tablets to help them take over phone numbers.
A young man sits in a car, pointing a cellphone camera out of the window, seemingly trying to remain undetected. As he breathes heavily in anticipation, he peers at a T-Mobile store across the road from where he is parked.
Suddenly, there is some commotion inside. An accomplice grabs something off a table where a T-Mobile employee is sitting. The accomplice, dressed in a mask and black baseball cap, then bursts out of the store and clumsily sprints towards the car.
The man in the vehicle starts laughing, then giggling uncontrollably like a child. The pair got what they came for: a T-Mobile employee’s tablet, the sort workers use every day when dealing with customer support issues or setting up a new phone.
To the people in the car, what this tablet is capable of is much more valuable than iPad hardware itself. The tablet lets them essentially become T-Mobile. It can grant them the ability to take over target phone numbers, and redirect any text messages or calls for the victim to the hacker’s own device, as part of a hack called a SIM swap. From there, they can easily break into email, cryptocurrency, and social media accounts.
For years SIM swappers have used social engineering to trick telecom employees into porting phone numbers. Or they’ve turned to malicious insiders at telecoms to perform the swaps on their behalf. One sometimes overlooked technique of SIM swappers is much more physical: going into the store and seizing the tablets themselves, like the incident shown in the video obtained by 404 Media. The technique appears to have fallen out of favor as T-Mobile introduced more security protections, but still provides insight into the lengths that SIM swappers will go to.
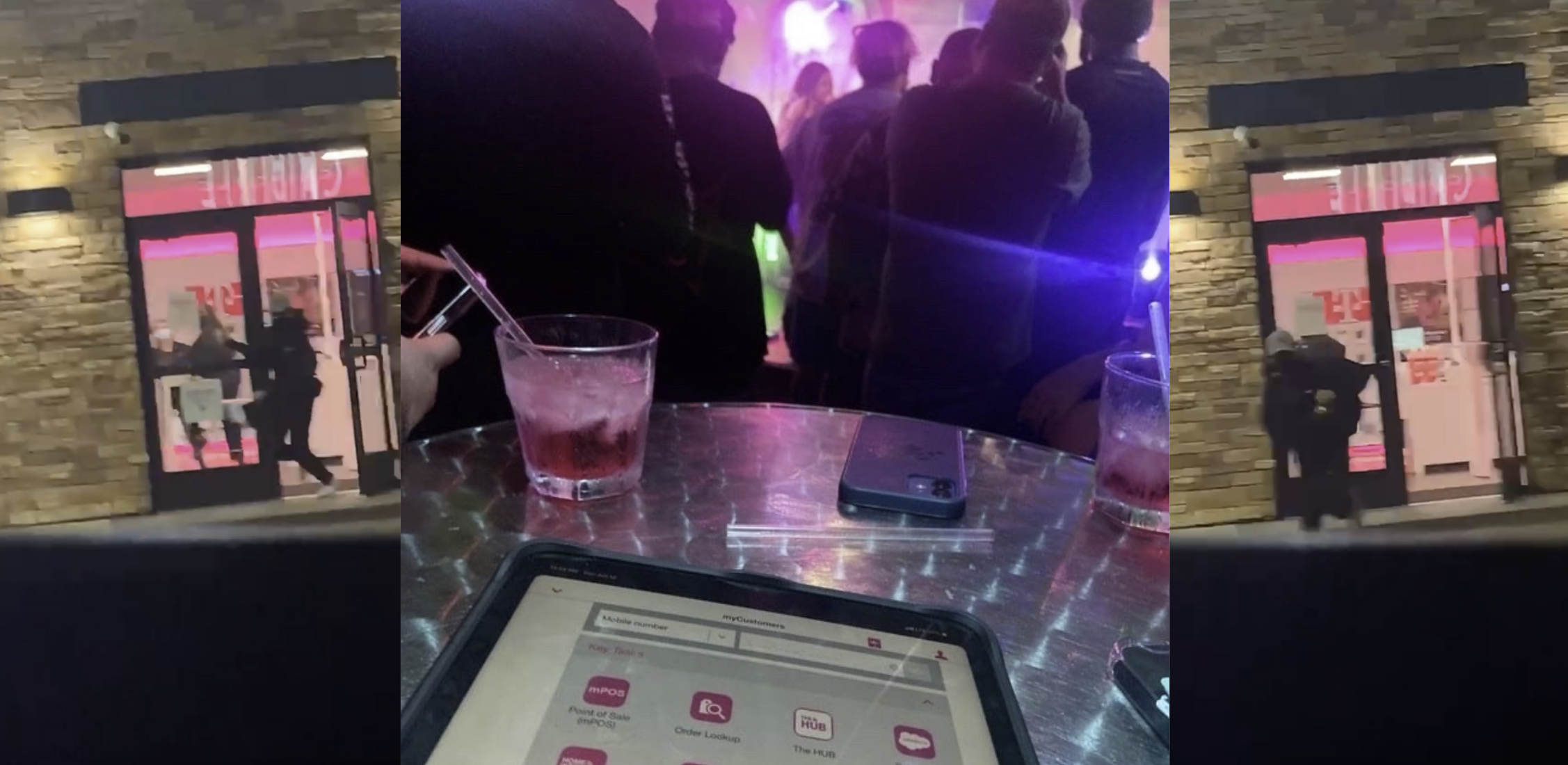
A separate photo also obtained by 404 Media shows someone flexing their acquisition of such a tablet. In the photo, it sits on a table in what appears to be a nightclub or other venue, surrounded by drinks.
As one person who called themselves “Drew” told the cybersecurity podcast Darknet Diaries in 2022, “T-Mobile is the easiest place to hit right now. You go to a T-Mobile, you run in, you take the store manager’s tablet from his hands; you run out.” Drew described the technique as “remo snatching,” with remo being short for remote tablet, and the podcast explained that thieves may only have 10 minutes or so to do a swap before T-Mobile shuts down the tablet.
According to another photo of a T-Mobile tablet, the onboard software provides various options such as “Point of Sale (mPOS),” “Order Lookup,” and “Process DASH Returns.” One of the apps, called “Tapestry,” is what T-Mobile uses to work with customers’ accounts, and which SIM swappers in turn use to take over numbers, according to a post from a security researcher who goes by the moniker n0sec. “From my interviews with those who have done this, they say that you ask to buy a prepaid SIM card and they will put the remo in your hands, for you to type some billing information. This is the point where you run,” they write. The thieves then use a manager, or “manny,” login that has been previously phished, which then grants them the necessary privileges to perform SIM swaps, n0sec adds.
It appears remo snatching is becoming less common. In their own post, n0sec said that T-Mobile now requires a manager login and a second piece of authorization. And in a statement to 404 Media, T-Mobile mentioned its implementation of “new enhancements.”
“Like every retailer, we experience theft in our stores from time to time and so we have prevention and response controls in place to help protect customers and employees,” the statement read. “This includes the ability to disable stolen devices. As criminals evolve their methods, so do we and we continue to implement new enhancements.”
link: https://www.404media.co/how-hackers-straight-up-steal-t-mobile-tablets-to-sim-swap/
deleted by creator
Removed by mod
To be fair, it might be unwise to publicise the issue if it was still a major problem. That might just cause copycats.
still a good story to tell people who are designing a security infrastructure, they need to think about things like this
Credentials of that device will be blocked within minutes after such incidents if the company is any capable.
OK, it’s the fucking Bundespost so they probably will not be capable. Idiots.
This reads like one of those articles made to scare old people.
“remo, short for ‘remote tablet’”
Why do I think the interviewer just heard them saying remote in a strong accent?
Surely these tablets are enrolled in some MDM (AirWatch, Soti, MobileIron, etc.) They could be locked down or remotely wiped in a matter of minutes.
I mean, the full article was even copied into the post.
thieves may only have 10 minutes or so to do a swap before T-Mobile shuts down the tablet.
You can’t “SIM swap” a cryptocurrency account, only custodial services.
Exactly, but unfortunately to most people crypto is buying bitcoin on coinbase and be like “i bought bitcoin”. No, you didnt. Also, anybody who knows better would never use sms OTP on these accounts. Thats just begging to be targeted.